Table of Contents
Introduction
What is Cybersecurity: Nowadays, it is impossible not to hear about this on the Internet and how our bank details, personal files, or computers can also be hacked. So protecting our digital space is crucial. Cybersecurity in companies is just as critical or even more so than in the private sphere. Therefore, your company’s digital assets must be protected against external threats.
Discover cybersecurity solution that protect every part of your IT environment, from your cloud solutions, data and networks to end-user devices.
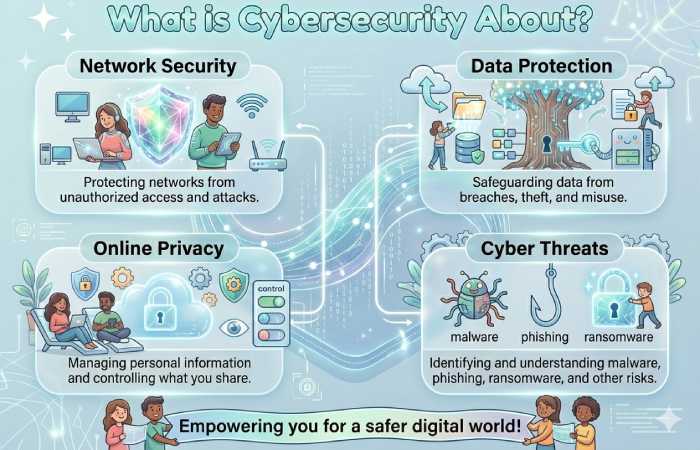
What is Cybersecurity?
By cybersecurity, we understand those strategies and actions a company or individual carries out to protect and defend their digital assets from possible it attacks, such as information theft and device control.
It is a branch of computing that is increasingly necessary since our level of online connection is increasingly higher and more frequent. Specifically, cyber attacks are a constant threat to companies of all sizes.
It is not only necessary to protect the computer equipment but also the network connections. Any technological device can and should be protected against these possible threats. Especially if they have access to personal, banking, or company data.
What is Cybersecurity About?
A successful cybersecurity approach has multiple sheets of protection spread across the computers, networks, programs, or data one intends to keep safe. In an organization, people, processes, and technology must complement each other to create an effective defense against cyberattacks. A unified threat management structure can automate integrations between select Cisco security products and accelerate essential security operations functions: detection, investigation, and remediation.
1. People
Users should understand and follow basic data security principles, such as choosing strong passwords, being cautious with email attachments, and backing up data. Learn more about basic cybersecurity principles.
2. Processes
Organizations must have a structure in place to handle suspected and attempted cyberattacks. A reputable facility can guide you and explain how you can identify attacks. Protect systems, detect and respond to threats, and recover from successful attacks. See the video explanation of the NIST Cybersecurity Framework.
3. Technology
Technology is necessary to provide organizations and individuals with the information security tools to protect themselves from cyber attacks. Three important entities must be protected: endpoint devices (such as computers, smart devices, and routers), networks, and the cloud and standard technologies that protect these entities include next-generation firewalls, DNS filtering, malware protection, antivirus software, and email security solutions.
Types of Cybersecurity
A good cybersecurity strategy for companies or individuals should focus on three main objectives: Attack prevention, threat detection, and recovery.
| Cybersecurity Type | Example Tools | Typical Price | Reviews / Ratings |
| Network Security | Firewalls, IDS/IPS, VPN | Fortinet FortiGate: ₹20,000–₹40,000+ hardware; VPN services vary | High enterprise adoption; strong protection |
| Endpoint Security | CrowdStrike Falcon, SentinelOne | Falcon ~ ₹700–₹900 /endpoint/mo; SentinelOne ~ ₹6,000–₹8,000/endpoint/yr | Falcon ~4.7/5; SentinelOne ~4.8/5 (G2) |
| Cloud Security | Prisma Cloud, Microsoft Defender for Cloud | Varies (cloud provider billing) | Strong posture management & compliance |
| Application Security | Burp Suite, OWASP ZAP | Burp Pro ~ ₹35,000/yr; OWASP ZAP Free | Burp Suite ~4.7/5 |
| Vulnerability Scanning | Nessus Professional | ₹2,60,000–₹2,90,000/yr | ~4.6/5 |
| Penetration Testing | Metasploit | Free / Pro ~ ₹1,20,000+/yr | 4.5/5 |
| Antivirus / Threat Protection | Norton 360, Bitdefender | Norton ~ ₹4,000/yr; Bitdefender ~ ₹3,000/yr | ~4.5/5 |
| SIEM (Log & Event Management) | Splunk | Custom Pricing | ~4.5/5 (G2) |
| Managed Detection & Response (MDR) | Secureworks, Arctic Wolf | ~₹4,500–₹35,000+/mo (enterprise) | Good for continuous monitoring |
| Identity & Access Management (IAM) | Okta, Azure AD | Okta ~ ₹2,500–₹4,000/user/yr | Critical for Zero Trust |
| Data Security & DLP | Palo Alto DLP / Prisma Cloud | Custom Pricing | Allied with compliance and classification |
Why is Cybersecurity Important?
In today’s joined world, everyone benefits from advanced cyber defense programs. At the individual stage. A cyber-security attack can result in everything from identity theft to extortion attempts and the loss of essential data, such as family photos. In addition to everyone relies on critical infrastructures such as power plants, hospitals, and financial services companies. Hence, Protecting these and other organizations is essential to the functioning of society.
Everyone profits from the work of cyber threat researchers and also Like Talos’ team of 250 threat researchers, who investigate new and emerging threats and cyberattack strategies and also they reveal new resistances, educate the public on the importance of security, and strengthen open source tools. His work makes the Internet safer for everyone.
How To Learn Cyber Security
Understand the Basics
Before diving into tools and hacking, you need a solid foundation:
- Key Concepts:
- CIA Triad: Confidentiality, Integrity, Availability
- Threats vs. Vulnerabilities
- Malware types: viruses, ransomware, spyware, worms
- Networking basics: TCP/IP, DNS, HTTP/S, VPNs
- Recommended Resources:
- Cybrary – Intro to Cybersecurity
- Coursera – Cybersecurity Fundamentals
- Books: “Cybersecurity For Beginners” by Raef Meeuwisse
Learn Networking & Operating Systems
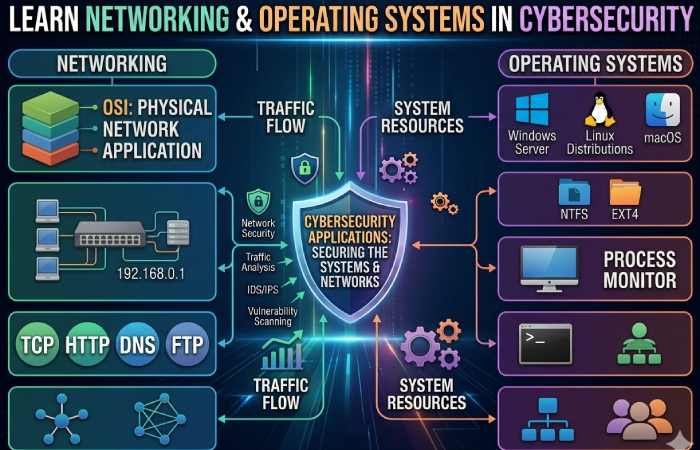
Cybersecurity relies heavily on networks and operating systems:
- Networking Skills:
- Subnetting, routing, firewall rules
- Packet analysis
- Network protocols (TCP, UDP, ICMP)
- Operating Systems:
- Windows security policies and permissions
- Linux: shell commands, file permissions, network configurations
- Virtualization (VMware, VirtualBox)
- Resources:
- Cisco Networking Academy
- Linux Foundation – Intro to Linux
Hands-On Labs & Simulations
Practice is critical. Set up virtual labs to experiment safely:
- Lab Environments:
- VirtualBox / VMware for isolated testing
- TryHackMe and Hack The Box for structured challenges
- Cyber Range platforms for real-world scenarios
- Tools to Learn:
- Wireshark, Nmap, Metasploit, Burp Suite
- Security Onion for monitoring and detection
- Resources:
- TryHackMe
- Hack The Box
- OverTheWire – Wargames
Specialized Areas in Cybersecurity
Once comfortable with basics, explore these specialized domains:
| Domain | What to Learn | Resources |
| Ethical Hacking / Penetration Testing | Vulnerability scanning, exploitation, reporting | CEH – Certified Ethical Hacker |
| Cloud Security | AWS, Azure, GCP security, IAM, CloudTrail | AWS Security Learning |
| Application Security | Secure coding, OWASP Top 10, threat modeling | OWASP |
| Incident Response & Forensics | Log analysis, malware investigation, root cause analysis | SANS Cybersecurity Training |
| SOC Analyst / Threat Hunting | SIEM, monitoring, alerts, threat intelligence | Splunk Training |
Get Certified (Optional but Recommended)
Certifications help validate your skills for employers:
- Entry Level:
- CompTIA Security+
- EC-Council CEH (Certified Ethical Hacker)
- Intermediate:
- CISSP (Certified Information Systems Security Professional)
- CompTIA Cybersecurity Analyst (CySA+)
- Advanced / Specialized:
- Offensive Security Certified Professional (OSCP)
- GIAC Certifications (GSEC, GCIH)
Stay Updated
Cybersecurity evolves daily. Keep learning:
- Follow blogs and news sites:
- Krebs on Security
- The Hacker News
- Join communities: Reddit, Discord, LinkedIn groups
- Participate in CTFs (Capture the Flag competitions)
Suggested Learning Path (Timeline)
| Stage | Focus | Estimated Time |
| Beginner | Basics, networking, OS | 2–3 months |
| Intermediate | Labs, tools, hands-on hacking | 3–6 months |
| Advanced | Specialization, certifications | 6–12 months |
| Continuous | Threat updates, CTFs, community engagement | Ongoing |
Cybersecurity Tools
| Tool | Category / Best For | Price (Typical) | Review / Rating |
| CrowdStrike Falcon | EDR / Endpoint Protection | ~$8.99/endpoint/month (SMB tiers); enterprise custom | 9.6 / top EDR platform |
| SentinelOne Singularity | EDR / Autonomous Response | ~$6.99/endpoint/month; ~75‑100 USD/endpoint/yr (small Biz) | 9.4 / autonomous threat response |
| Microsoft Defender XDR | XDR / Native Microsoft Security | ~$3/user/month (business) | 9.2 / strong built‑in protection |
| Palo Alto Cortex XSIAM | SIEM / XDR Orchestration | Custom pricing (enterprise) | 9.1 |
| Darktrace | Network Defense (NDR) | Custom pricing | 9.5 |
| Fortinet FortiGate | Firewall / Network Security | ~$400–$500 hardware | 4.5 / strong NGFW |
| Bitdefender Total Security | Antivirus / Multi‑layer Protection | ~$34.99‑$49.99/yr (5 devices) | ~4.5/5 on reviews |
| Norton 360 Deluxe | Antivirus + VPN + Dark‑Web Monitoring | ~$49.99/yr (standard) | ~4.5/5 reviews |
| Malwarebytes Premium | Malware & Ransomware Protection | ~$39.99/yr (individual) | Effective deep‑scan tool |
| ESET NOD32 / ESET Protect | Threat Detection / Antivirus | ~$39.99/yr | Reliable, lightweight |
| Nessus Professional | Vulnerability Scanning | ~$2,390–$3,500+/year | ~4.6/5 |
| Wireshark | Network Packet Analysis | Free | ~4.7/5 |
| Metasploit Framework | Penetration Testing | Free / Pro starts ~$1,500+/yr | ~4.5/5 |
| Check Point Harmony | Unified Security Platform | ~$50/user/year | ~4.6/5 |
| Trend Micro Deep Security | Virtual & Cloud Security | ~$200+/yr | ~4.6/5 |
| Sophos Intercept X | EDR / Small Biz Preferred | ~$28/user/yr | ~8.6/10 |
Best Practices for Cybersecurity
Cybersecurity best practices are proactive measures and strategies to prevent unauthorized access, data breaches, and cyber attacks. They cover people, processes, and technology, forming a holistic defense.

Strong Passwords & Identity Management
- Use complex passwords: Minimum 12 characters, mix of letters, numbers, symbols.
- Enable Multi-Factor Authentication (MFA): Adds an extra layer of security beyond passwords.
- Password managers: Use trusted tools to generate and store credentials securely.
Tools: LastPass, 1Password, Bitwarden
Tip: Avoid reusing passwords across accounts.
Software & System Updates
- Regularly patch operating systems, applications, and devices.
- Enable automatic updates whenever possible.
- Remove or disable unused software to reduce attack surface.
Best Practice: Apply critical security patches within 48–72 hours of release.
Network Security
- Firewalls: Deploy next-generation firewalls for network traffic filtering.
- Secure Wi-Fi: Use strong encryption (WPA3) and hidden SSID for corporate networks.
- Segment networks: Separate sensitive systems from general access networks.
- VPN usage: Encrypt data for remote workers or external access.
Tools: Fortinet, Cisco ASA, Palo Alto Networks
Endpoint Protection
- Install and maintain antivirus, anti-malware, and EDR solutions.
- Regularly scan devices for vulnerabilities.
- Use device encryption for sensitive data.
Tip: Include all laptops, mobile devices, and IoT devices in endpoint security policies.
Secure Cloud Practices
- Identity and Access Management (IAM): Control user permissions carefully.
- Data encryption: Encrypt data both at rest and in transit.
- Monitor cloud activity: Use cloud security posture management (CSPM) tools.
Tools: AWS Security Hub, Microsoft Defender for Cloud, Palo Alto Prisma Cloud
Data Backup & Recovery
- Implement regular backups of critical data.
- Store backups offline or in a secure cloud environment.
- Test disaster recovery plans periodically.
Tip: Follow the 3‑2‑1 rule: 3 copies of data, 2 different media, 1 off-site.
Employee Awareness & Training
- Conduct cybersecurity awareness programs regularly.
- Educate employees about phishing, social engineering, and safe browsing habits.
- Simulate phishing attacks to train employees in real-world scenarios.
Tip: Security is only as strong as your weakest link—often human error.
Incident Response Plan
- Prepare a documented incident response plan (IRP).
- Include detection, containment, eradication, recovery, and communication procedures.
- Assign roles and responsibilities for rapid response.
Tools: Splunk, Palo Alto Cortex XSOAR, IBM Resilient
Logging, Monitoring & Threat Detection
- Enable detailed logging of all network and system activity.
- Use SIEM (Security Information and Event Management) to detect anomalies.
- Monitor for signs of compromise like unusual logins or system changes.
Tools: Splunk, ELK Stack, LogRhythm
Compliance & Regulations
- Follow relevant cybersecurity standards:
- ISO 27001: Information Security Management
- NIST CSF: Risk-based framework
- GDPR / HIPAA: Regulatory compliance for sensitive data
Tip: Compliance does not equal security—it ensures baseline practices.
Secure Development Practices (For DevOps & Apps)
- Follow secure coding guidelines (OWASP Top 10).
- Conduct regular code reviews and penetration testing.
- Implement DevSecOps to integrate security into the software development lifecycle.
Regular Risk Assessments
- Identify critical assets and potential threats.
- Conduct vulnerability scanning regularly.
- Prioritize mitigation based on risk impact and probability.
Tools: Nessus, Qualys, OpenVAS
Cybersecurity Trends in 2026
| Trend | Description | Source / Link |
| AI‑Driven Attack & Defense | Artificial Intelligence is now a dual‑use technology — attackers use AI for automated phishing, adaptive malware, and reconnaissance while defenders use AI/ML for advanced anomaly detection and real‑time response. | Global Cybersecurity Outlook 2026 – WEF |
| Identity‑Centric Security & IAM Adaptation | Identity security becomes core — with credential abuse as a top attack vector. Identity Threat Detection and Response (ITDR) and IAM evolve to handle risk from humans and AI agents alike. | Sherweb: Identity‑first & ITDR Trend |
| Zero Trust Expansion | Zero Trust architecture extends beyond networks to cover users, devices, applications, and data — enforcing continuous verification. | Gartner Cybersecurity Trends 2026 |
| Post‑Quantum Cryptography & Quantum Readiness | Quantum computing is pushing organizations to prepare quantum‑resistant cryptography and transition planning to avoid “harvest now, decrypt later” threats. | Gartner on Postquantum Cryptography |
| Cyber Resilience over Prevention | Focus shifts from simply preventing breaches to ensuring quick detection, response, business continuity, and recovery capability — measured by resilience outcomes. | INE Top 5 Cybersecurity Trends 2026 |
| Geopolitical Threat Integration | Cybersecurity strategies now explicitly account for geopolitical risk (state‑linked attacks, espionage, infrastructure targeting) as part of risk planning. | Global Cybersecurity Outlook 2026 – WEF |
| Supply Chain & Software Bill of Materials (SBOM) | Full supply chain visibility becomes essential — vulnerabilities in software dependencies can cascade into broader attacks, requiring continuous monitoring and vendor security assurance. | Splashtop: Supply Chain Assurance |
Conclusion
Cyber-security, or information technology security, protects your computer and networks from disclosing information. It also safeguards your computer system from theft and damage to its hardware, software, or electronic data. It also prevents disruption or misdirection of the services they provide

